Yesterday -- 06 November 2006, Melbourne, Australia time -- enhanced versions of two of our free Lotus Notes applications were released. They have been in beta testing release mode for a month or so.
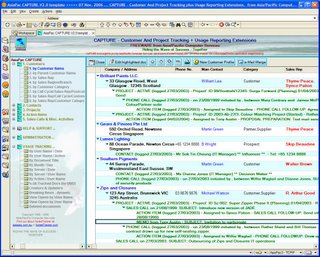
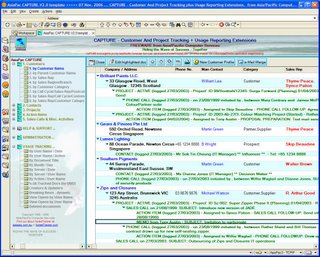
CAPTURE Version 2.0 is a free CRM database. The name stands for "Customer And Project Tracking plus Usage Reporting Extensions" with the usage reporting being via a built-in copy of our unique NotesTracker database usage reporting tool.
As well as numerous smaller changes, this new version of CAPTURE includes a "
mail merge" function so that you can now easily merge any of your mail memo documents (from your Notes mail Inbox view) anywhere into the hierarchy of CAPTURE documents. This is a significant new way to incorporate information about your customers and prospects into a CAPTURE database.
As well as this, CAPTURE Version 2.0 also has a full set of NotesTracker views built in, so that you can now choose the "internal logging" capability of NotesTracker to store all your tracking documents into the CAPTURE database itself rather than in an external NotesTracker Repository database.
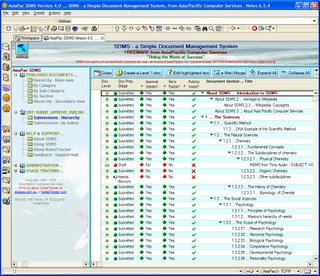
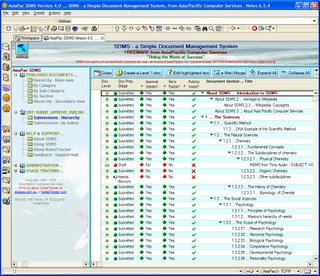 SDMS
SDMS -- the Simple Document Management System -- now also has the same handy "
mail merge" function, together with a major new "
publishing life cycle" capability so that instead of just (as previously) being able to create/edit/submit documents, they must now be approved and finally be released for publishing.
According to the SDMS design philosophy, the publishing steps are designed to be simple to carry out.
Of course, as before SDMS has our powerful NotesTracker usage tracking capability built in.
Note: If you happened to download SDMS Version 4.0 yesterday, please be aware that there's already an updated version 4.01 available! It released this less than an hour ago this morning (07 November 2006, Melbourne time). An enhancement was made to the way that editing of the SDMS Database Profile Document is managed.
You'll find links to both the SDMS and the CAPTURE download pages on our web site's home page: that is, either
asiapac.com.au or its mirror
notestracker.com